If you’re a Linux system administrator, chances are you’ve got more than one machine that you’re responsible for on a daily basis. You may even have a bank of machines that you maintain that are similar — a farm of Web servers, for example. If you have a need to type the same command into several machines at once, you can login to each one with SSH and do it serially, or you can save yourself a lot of time and effort and use a tool like ClusterSSH.
ClusterSSH is a Tk/Perl wrapper around standard Linux tools like XTerm and SSH. As such, it’ll run on just about any POSIX-compliant OS where the libraries exist — I’ve run it on Linux, Solaris, and Mac OS X. It requires the Perl libraries Tk (perl-tk on Debian or Ubuntu) and X11::Protocol (libx11-protocol-perl on Debian or Ubuntu), in addition to xterm and OpenSSH.
Installation
Installing ClusterSSH on a Debian or Ubuntu system is trivial — a simple sudo apt-get install clusterssh will install it and its dependencies. It is also packaged for use with Fedora, and it is installable via the ports system on FreeBSD. There’s also a MacPorts version for use with Mac OS X, if you use an Apple machine. Of course, it can also be compiled from source.
In order to generate a key, we will use a tool called ssh-keygen.Open Terminal on Linux or Mac, or Git Bash on Windows. Enter the following: ssh-keygen -t rsa -C 'your_email_address@example.com' After you have entered this command you will be asked where to save the key. Your Red Hat account gives you access to your profile, preferences, and services, depending on your status. Register If you are a new customer, register now for access to product evaluations and purchasing capabilities.
Configuration
ClusterSSH can be configured either via its global configuration file — /etc/clusters, or via a file in the user’s home directory called .csshrc. I tend to favor the user-level configuration as that lets multiple people on the same system to setup their ClusterSSH client as they choose. Configuration is straightforward in either case, as the file format is the same. ClusterSSH defines a “cluster” as a group of machines that you’d like to control via one interface. With that in mind, you enumerate your clusters at the top of the file in a “clusters” block, and then you describe each cluster in a separate section below.
For example, let’s say I’ve got two clusters, each consisting of two machines. “Cluster1” has the machines “Test1” and “Test2” in it, and “Cluster2” has the machines “Test3” and “Test4” in it. The ~.csshrc (or /etc/clusters) control file would look like this:
Entity Relationship Diagram Software Engineering While designing a conceptual data model, you should use appropriate software. For instance, ConceptDraw DIAGRAM v12 is a user-friendly ER diagram tool that has a lot of samples and templates to facilitate your work. The Most Popular Mac ER Diagram Software Experience an easy way to create entity relationship diagram on Mac, Windows and Linux. Apple users can make high-quality ER diagram with ease in the OS X platform. Share or cooperate on files effectively through Cloud. Download Mac Version. SQLEditor for Mac OS v.1.6.8 An SQL database design and entity relationship diagram (ERD) tool. - SQLEditor replaces typing SQL by hand with dragging, dropping and clicking. It makes creating databases faster and easier. How to create erd diagram.
clusters = cluster1 cluster2
cluster1 = test1 test2
cluster2 = test3 test4
You can also make meta-clusters — clusters that refer to clusters. If you wanted to make a cluster called “all” that encompassed all the machines, you could define it two ways. First, you could simply create a cluster that held all the machines, like the following:
clusters = cluster1 cluster2 all
cluster1 = test1 test2
cluster2 = test3 test4
all = test1 test2 test3 test4
However, my preferred method is to use a meta-cluster that encompasses the other clusters:
clusters = cluster1 cluster2 all
cluster1 = test1 test2
cluster2 = test3 test4
all = cluster1 cluster2
By calling out the “all” cluster as containing cluster1 and cluster2, if either of those clusters ever change, the change is automatically captured so you don’t have to update the “all” definition. This will save you time and headache if your .csshrc file ever grows in size.

Using ClusterSSH
Using ClusterSSH is similar to launching SSH by itself. Simply running cssh -l <username> <clustername> will launch ClusterSSH and log you in as the desired user on that cluster. In the figure below, you can see I’ve logged into “cluster1” as myself. The small window labeled “CSSH [2]” is the Cluster SSH console window. Anything I type into that small window gets echoed to all the machines in the cluster — in this case, machines “test1” and “test2”. In a pinch, you can also login to machines that aren’t in your .csshrc file, simply by running cssh -l <username> <machinename1> <machinename2> <machinename3>.
If I want to send something to one of the terminals, I can simply switch focus by clicking in the desired XTerm, and just type in that window like I usually would. ClusterSSH has a few menu items that really help when dealing with a mix of machines. As per the figure below, in the “Hosts” menu of the ClusterSSH console there’s are several options that come in handy.
“Retile Windows” does just that if you’ve manually resized or moved something. “Add host(s) or Cluster(s)” is great if you want to add another set of machines or another cluster to the running ClusterSSH session. Finally, you’ll see each host listed at the bottom of the “Hosts” menu. By checking or unchecking the boxes next to each hostname, you can select which hosts the ClusterSSH console will echo commands to. This is handy if you want to exclude a host or two for a one-off or particular reason. The final menu option that’s nice to have is under the “Send” menu, called “Hostname”. This simply echoes each machine’s hostname to the command line, which can be handy if you’re constructing something host-specific across your cluster.
Caveats with ClusterSSH
Like many UNIX tools, ClusterSSH has the potential to go horribly awry if you aren’t very careful with its use. I’ve seen ClusterSSH mistakes take out an entire tier of Web servers simply by propagating a typo in an Apache configuration. Having access to multiple machines at once, possibly as a privileged user, means mistakes come at a great cost. Take care, and double-check what you’re doing before you punch that Enter key.
Conclusion
ClusterSSH isn’t a replacement for having a configuration management system or any of the other best practices when managing a number of machines. However, if you need to do something in a pinch outside of your usual toolset or process, or if you’re doing prototype work, ClusterSSH is indispensable. It can save a lot of time when doing tasks that need to be done on more than one machine, but like any power tool, it can cause a lot of damage if used haphazardly.
Connect to a server by using SSH on Linux or Mac OS X
This article provides steps for connecting to a cloud server froma computer running Linux® or MacOS® X by using Secure Shell (SSH).It also discusses generating an SSH key and adding a public key tothe server.
Introduction
SSH is a protocol through which you can access your cloud server and runshell commands. You can use SSH keys to identify trusted computers withoutthe need for passwords and to interact with your servers.
SSH is encrypted with Secure Sockets Layer (SSL), which makes it difficultfor these communications to be intercepted and read.
Note: Many of the commands in this article must be run on your localcomputer. The default commands listed are for the Linux command line orMacOS X Terminal. To make SSH connections from Windows®, you can use a clientsimilar to the free program, PuTTY.To generate keys, you can use a related program, PuTTYGen.
Log in
Using the Internet Protocol (IP) address and password for your cloud server, log in byrunning the following ssh command with username@ipaddress as the argument:
The system prompts you to enter the password for the account to which you’reconnecting.
Remote host identification
If you rebuilt your cloud server, you might get the following message:
One of the security features of SSH is that when you log in to a cloudserver, the remote host has its own key that identifies it. When you tryto connect, your SSH client checks the server’s key against any keysthat it has saved from previous connections to that IP address. After yourebuild a cloud server, that remote host key changes, so your computerwarns you of possibly suspicious activity.
To ensure the security of your server, you canuse the web console in the Cloud Control Panel to verify your server’s new key.If you’re confident that you aren’t being spoofed, you can skip thatstep and delete the record of the old SSH host key as follows:
On your local computer, edit the SSH known_hosts file and remove anylines that start with your cloud server’s IP address.
Ij network tool for mac os x. Canon IJ Network Tool Download for OS Windows, Mac, OS X, and Linux – Canon Network Tool Instrument Source usually is a software system developed by Canon. A system which is scheduled to become involved with Home windows Celebration Scheduler to start out the program at the scheduled times (different packages decided through the model). Canon IJ Network Tool Download Ver.4.7.0 (Mac) for OS Mac – Canon IJ Community (Canon IJ Network Tool) Instrument Source is usually a software system developed by Canon.A system which is scheduled to become involved in Home windows Celebration Scheduler to start out the program at the scheduled times (different packages decided through the model). Canon IJ Network tool for Mac OS X – Canon Support Download August 18, 2018 By Mochi Mochi Canon IJ Network Tool for Mac OS X Download – The following picture display on the menu and the items displayed on the display means of the Canon IJ Network. Canon IJ Network Tool is a free application that allows you to install on your laptop or computer, view or configure the network settings of your printer is connected via a network. Canon IJ Network Tool is a cross-platform and works on the operating system Mac OS X and Windows.For Operating System / Platform Windows binaries are available in the form can be downloaded at this link.
Note: Use the editor of your choice, such as nano on Debian or Ubuntu serversor vi on RPM or CENTOS servers. For simplicity, this article just uses nano. If you prefer to use vi,substitute vi for nano in the edit commands.For more on using nano, seehttps://support.rackspace.com/how-to/modify-your-hosts-file/.
If you are not using Linux or MacOS X on your local computer, thelocation of the known_hosts file might differ. Refer to your OS forinformation about the file location. PuTTY on Windows gives you theoption to replace the saved host key.
Generate a new SSH key pair
You can secure SSH access to your cloud server against brute forcepassword attacks by using a public-private key pair. A public key is placed onthe server and a matching private key is placed on your local computer. If youconfigure SSH on your server to accept only connections using keys,then no one can log in by using just a password. Connecting clientsare required to use a private key that has a public key registered onthe server. For more on security, reviewLinux server security best practices.
Use the following steps to generate an SSH key pair:
Run the following command using your email address as a label.Substitute your email address for
your_email@example.cominthe command.A message indicates that your public-private RSA key pair isbeing generated.
At the prompt, press Enter to use the default location or entera file in which to save the key and press Enter.
If you want the additional security of a password for the key pair,enter a passphraseand press Enter. If you don’t want to use a passwordwith the key pair, press Enter to continue without setting one.
Your key pair is generated, and the output looks similar to the following example:
Optionally, add your new key to the local ssh-agent file to enableSSH to find your key without the need to specify its location everytime that you connect:
You can use an SSH configuration shortcut instead of the ssh-agent fileby following the instructions in the Shortcut configuration sectionlater in this article.
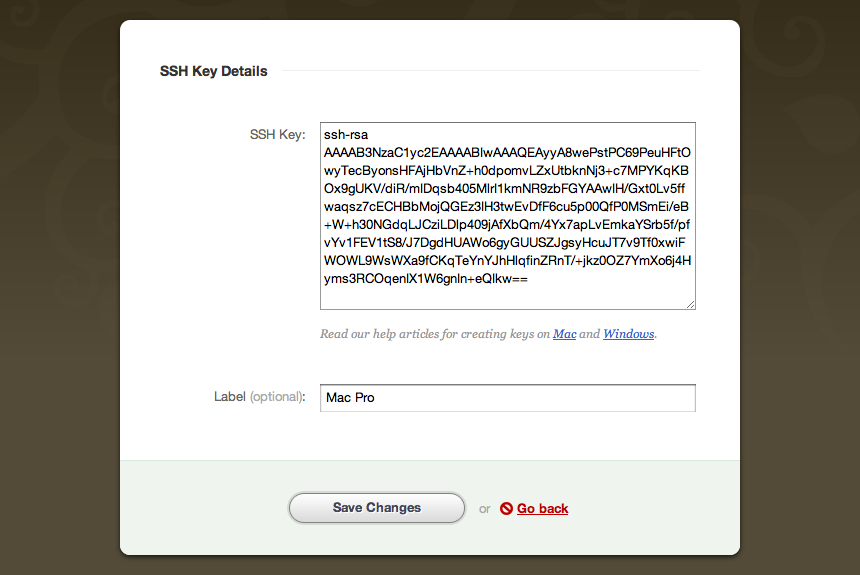
Add the public key to your cloud account
To make it easy to add your key to new cloud servers that you create,upload the public key to your cloud account by following these steps:
- Log in to the Cloud Control Panel.
- In the top navigation bar, click Select a Product > Rackspace Cloud.
- Select Servers > SSH Keys.
- Click Add Public Key.
- Enter a key name, such as Work Laptop, to remind you which computer this key is for.
- Select the region for which you want to store the public key. Tostore your key in multiple regions, repeat these steps foreach region. The key must reside in the same region as the server.
Paste the contents of the id_rsa.pub file that you created intothe Public Key field. You can get the file contents by eitheropening the file in a text editor or by running the followingcommand:
- Click Add Public Key.
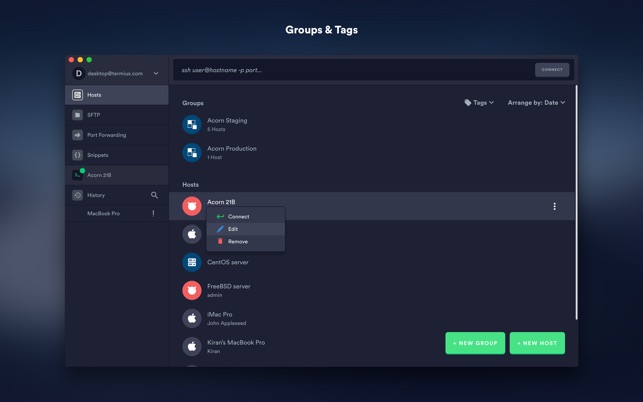
Free Ssh Tool For Mac
If you want to add the key manually, instead of by using the Control Panel, reviewLinux server security best practicesand use the following command:
Create a new server by using a stored key
Ssh Software For Mac
When you create a new cloud server, you can add a stored key to the newserver.
On the Create Server page, expand the Advanced Options section.
From the SSH Key menu, select your key from the list.
If you don’t see a stored key in the list, you can perform one of the following actions:
- Switch the region for the new server to the region where you have stored the SSH key.
- Repeat the steps in the preceding section, Add the public key to your cloud account,to add the key to the region in which you want to create the new server.
Add the key to an existing server
Ssh Tool For Mac To Redhatter
You can’t use the Cloud Control Panel to add a public key to anexisting server. Follow these steps to add the key manually:
On your cloud server, create a directory named .ssh in the homefolder of the user that you connect to by using SSH.
Create or edit the authorized_keys file and add your public key tothe list of authorized keys by using the following command:
A key is all on one line, so ensure that the key isn’t broken byline breaks. You can have multiple keys in the authorized_keysfile, with one key per line.
Set the correct permissions on the key by using the following commands:
If you have any issues and need to fix permissions issues, run the following comand:
After you have added the public key to the authorized_keys, you can make an SSHconnection by using your key pair instead of the account password.
Shortcut configuration
Use the following instructions to set up a connection shortcut by creating a~/.ssh/config file on your local computer and adding your server and keydetails to it.
Using a text editor, add the following text to the ~/.ssh/config file, changing thevalues to match your server information:
Each of the following entries describes a feature of the server:
- Host: A shortcut name that you use to tell SSH to use thisconnection.
- HostName: The address of the server to which you connect.
- User: The name of the user account to connect to on theserver.
- IdentityFile: The location of the private key file (id_rsa).
After you set up the config file, connect to the server by usingthe following command with your shortcut name:
Troubleshooting
If you have trouble making a new connection after you restart theserver, use the following steps to help you resolve the issue:
The best way to troubleshoot SSH or SFTP login issues is to attempt tologin through SSH while logged into the Emergency Console and to watch the log,which typically includes the reason for a failure. If no reason is given,it could be a firewall issue. For RPM servers, run the following command to watch the log:
For Debian servers, run the following command to watch the log:
- If you get a
connection timeouterror, check the IP address thatyou used to ensure that it’s correct. You might also check theserver’s iptables to ensure that it isn’t blocking the port used by SSH. - If you get a
connection refusederror, you might be trying to useSSH with the wrong port. If you changed your server to listen to aport other than 22, use the-poption with SSH to specifythe port. - If your login is rejected, then you might have an issuewith your key. Change the
sshdconfiguration to allow passwordconnections by settingPasswordAuthenticationtoyes. Restartthe server and try again. If you connect after these changes, thenthe issue is with the key and you must verify that the key is in theright place on the server. If all else fails, review your changes and restart the SSH daemon onthe server by running the following command:
If you get a message that the SSH service is unknown, run thecommand with
sshdas the service name instead.
Experience what Rackspace has to offer.
Ssh Tool For Mac To Redhat Version
©2019 Rackspace US, Inc.
How To Ssh From Mac
Except where otherwise noted, content on this site is licensed under a Creative Commons Attribution-NonCommercial-NoDerivs 3.0 Unported License